Introduction
This is a multi-part series on getting Jasager to play nicely with Metasploit, Hamster & Ferret to create an evil wifi tar-pit of sorts. The end result will be a wireless network that can gather and replay session cookies for web applications and log passwords for a number of different protocols.
Building on Jasager and Metasploit to snare people in and trick their browsers into handing over session cookies, we take it a step further with Hamster & Ferret to actually hijack these active sessions.
Sidejacking
As I mentioned in my wireless/sidejacking defense article, sidejacking happens when you allow a session-id cookie to go across the wire in the clear. A third-party gets the session ID cookie and then proceeds to import the cookie into their browser, whereupon they have access to the account the session-id belongs to. This doesn't (usually) expose the password to the account, so access is usually temporary.
Sidejacking works best on a wired hub, open wireless networks, or in combination with some kind of man-in-the-middle attack. We're one better with Jasager and Metasploit. We are making a wide-open network where we are the default route and basically emulating every server in the planet for a variety of popular protocols.
Ferret
Ferret literally ferrets out interesting information from an interface. Kind of like tcpdump. For the intents of this article, Ferret's purpose is to watch the ethernet interface for session cookies while victims get directed to our fake web server which emulates various high-profile sites. As the fake web server gets these cookies, Ferret stores them for Hamster.
Hamster
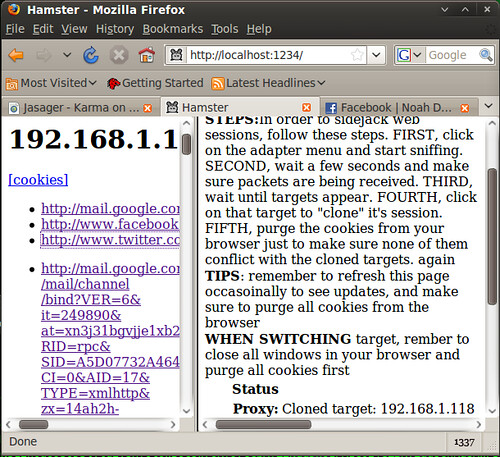
Hamster is little more than a plain http proxy. By default, it runs on localhost:1234. If you point your browser's http proxy to that address and then navigate to http://127.0.0.1:1234/ you will see a dashboard with statistics about what Ferret has gathered. This includes IP addresses that have been sidejacked.
What you need
Jasager and Metasploit, set up HiR Style
A Crossover Ethernet Cable
It helps if you have a some way to get out to the Internet at the same time all this stuff is running. In my case, I'm tethering with my LG Chocolate.
Install
Download, exrract and compile hamster/ferret from Errata Security.
Note: On Ubuntu, I had to install the package "libpcap-dev" to get ferret to compile.
$ wget http://hamster.erratasec.com/downloads/hamster-2.0.0.tar.z
$ tar xzf hamster-2.0.0.tar.z
$ cd ~/hamster/build/gcc4
$ make
$ cd ~/ferret/build/gcc4
$ make
Copy the Ferret Binary to the hamster/bin directory. I really wish Errata would streamline this crufty build process, but it works.
$ cp ~/ferret/bin/ferret ~/hamster/bin/Pulling it all together
Just like in part 2:
- Boot Jasager
- Connect the ethernet cable
- Set your laptop's ethernet interface for 192.168.1.2
- Try to ping Jasager.
- Start metasploit (as root) with the karma.rc file
$ cd ~/hamster/bin/
$ sudo ./hamster
Set your browser's http proxy to 127.0.0.1:1234 then navigate to http://127.0.0.1:1234. Click "Adapters" and type the interface name that Jasager is connected to. Usually, this is eth0. You should eventually see the packet count increasing.
Alternatively, in another browser window or tab, pull up the Jasager control panel at http://192.168.1.1:1471/ just to see if there is any blood in the water.
Evil
Once someone connects and tries to get to a web page with a fully-functional browser, you see the database and target count increment. You may have some useable cookies and an IP address (or several) available to clone. Click one of the IP addresses in the right pane and the left pane will fill up with the sites that have been visited. Since Metasploit forces a lot of iframes to load, you will have to examine and poke around to figure out which (if any) of those sites have valid sessions stored. I recommend that you first clear all your cookies before cloning any IP addresses and clearing cookies between changing IP addresses to clone.
Also, if you forgot to update your proxy settings, Hamster will appear to work, but none of the cookies will be loaded. If you have a lot of trouble with Hamster cloning clients, make sure the proxy is pointed to 127.0.0.1:1234. You may clone this setting across all your proxy variables (such as SOCKS, etc)
Here, as shown in the right-most tab, I have successfully sidejacked my Facebook account -- which I was logged into on another computer in the lab, before I shut it down and tried connecting to wifi with all of these elements running.
Now, if this doesn't open your eyes to the vulnerabilities in your employees' laptops, your own procedures, and what exactly you're opening yourself up to when you hit the road with your laptop and crack it open in a Panera, I don't know what else I can say to help it sink in.
Props
Robert Graham at Errata, for hacking and coding this simple and hackish tool. Follow Robert, Marisa and David on the Errata Security Blog.




