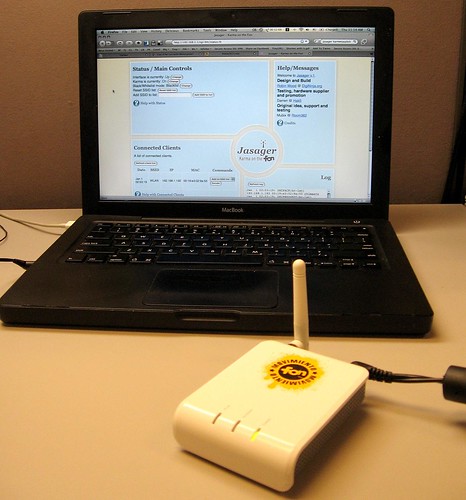
Meet Jasager, a mash-up of OpenWrt and Karma running on a La Fonera router. After seeing the Jasager walk-through on Darren Kitchen's website and then seeing Hak5 Season 4 Episode 5 (about 11 minutes into the episode), I had to give it a shot. If you can't tell, I've been lusting after Karmetasploit for quite a while.
Jasager doesn't provide the "evil" that metasploit offers (that is, the password-grabbing fake services, cookie-snarfing and browser exploiting parts), but Jasager DOES gleefully do the "Karma" part. No matter what SSID you try to connect to, Jasager will take your probe request and play the SSID back as a beacon. If the real access point is out of range or has a weaker signal than Jasager, it WILL rope you in. Mubix put together a post today with a lot of background to Jasager and where it's going. His ideas as well as Robin Wood's skills and Darren Kitchen's passion were a driving force in my interest in Karmetasploit from the get-go. This has been in the works for quite some time, as Darren couldn't stop gushing about it when I hung with him in Springfield. (Note to self: Fix the damn photos on that old post.)
The latest version of Metasploit Framework contains dozens of megabytes of code (mostly written in Ruby) and the La Fonera only has a few megabytes of flash for storing files, so setting up a full Karmetasploit ownage rig using a Fon isn't going to happen. That's not to say there isn't plenty of fun to be had. If you set this up on a public network, you can man-in-the-middle stuff with the Fon. Darren suggested using upside-down-ternet. You can do some hacking to make Jasager work with another full-fledged computer that can run Metasploit. The options are as limitless as your imagination even with a standalone Fon running Jasager. Be creative!
Now, on for some errata to Darren's howto:
I used OS X and command-line scp and ssh to do all the stuff Darren did with the windows equivalents. This is pretty straight-forward for command-line users.
In Step 8, you transfer 2 files into /tmp, but out.hex gets erased after the reboot in step 9 and before you're told to use it in step 10. So just SCP it over after the reboot in step 9.
I actually bricked my Fon at step 11 (where you use some goofy Windows GUI to flash the Fon). Fortunately, the walk-through enables RedBoot over Telnet early on. If you're not running Windows, then set up a tftp server on a workstation on an internet-separated network. I just used an ethernet cable to my MacBook. You can flash the firmware to the Fon via RedBoot with these instructions I got from the Fonera section of the OpenWrt Wiki.
Preparation for flashing:
La Fonera will use 192.168.1.1 and 192.168.1.254, so set your Ethernet interface to something in the 192.168.1.2-253 range on the system that you will use to tweak the Fon. Make sure it's got a tftp server on that system as well. Make sure you have the openwrt-atheros-2.6-vmlinux.lzma and openwrt-atheros-2.6-root.squashfs files. Make sure the network is segregated from the Internet, and make sure no DHCP servers are on the network.
I was using Mac OS X, and used this TFTP configuration front-end to control OS X's built-in tftpd. Note: TFTP is NOT FTP and an FTP server won't work in place of tftpd.
Once I got the Fon un-bricked and OpenWRT installed via TFTP and RedBoot. all the steps from 12 on worked fine. Hopefully using the above help, you won't need Windows nor will you brick your Fon.
Asmodian X has at least one Fon to play with as well. We'll cover our various experiments with them and label the posts with fon.
2008-10-09
Jasager Lives! Muahahaha!
Posted by
Ax0n
blog comments powered by Disqus
Subscribe to:
Post Comments (Atom)




