As part of my presentation for B-Sides KC later this week, I decided to revive my Evil Wifi project for a demonstration. I'll post my presentation slides and some talking points this weekend. Since my daily-use laptop is a MacBook running Mac OS X Snow Leopard, I put this together for OS X. I do understand that OS X isn't free, but it works, and well. It's also something fun (and perhaps evil) you can do with that new netbook after turning it into a hackintosh, as so many friends of mine have done lately.
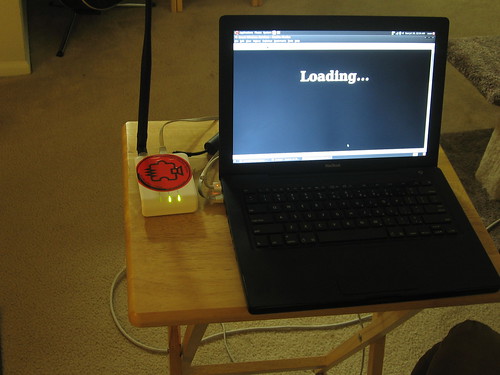
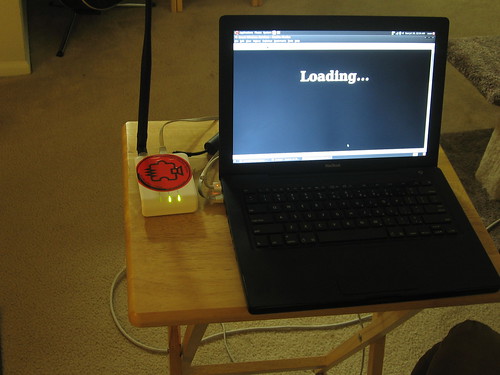
Originally, my Evil Wifi setup was a stand-alone rig with a laptop and a wireless router. The router has a tempting SSID for freeloaders (such as "Guest") while also running KARMA, a set of wireless driver modifications that will rope in any wireless devices that are broadcasting the names of their preferred networks in hopes of finding one to connect to. The router would hand out my laptop's IP as the DNS and default route.
The laptop was running Hamster and Ferret, a suite of sidejacking tools from Errata Security. These tools allow an attacker to gather and re-use session IDs from other network users. Additionally, it was running Metasploit for two reasons: a fake DNS server that resolves all domain names to itself, and a fake HTTP server with a specially-crafted page designed to facilitate the capture of many popular session cookies, which Hamster and Ferret would see and store.
Captive Portals are those wireless hotspots that require you to pay, enter a password, or acknowledge a terms-of-service agreement before continuing. No one could get out to the Internet through Evil Wifi. I intentionally designed the landing page to look like a captive portal that required a password. Most users would find themselves somewhat puzzled, then move on to a different network. Some people have asked if I could have configured the laptop to allow outbound traffic, and others (Like John Sawyer of Dark Reading) actually figured out how to do it. I thought about it last year, via Internet Connection Sharing, but I'd have lost the ability of Metasploit to gather a bunch of potentially valuable session IDs quickly.
I've been thinking of way to combine the best of both worlds, and I think I've nailed it.
To continue, you'll need a configuration much like the original Evil Wifi, but with a few tweaks. Here's how I did it using Mac OS X. Keep in mind that Linux works fine and also has Internet Connection Sharing, but you'll have to tweak some of the steps, and come up with equivalent iptables rule sets.
Laptop:
- MacBook, OS X Snow Leopard
- Metasploit Framework (Using build 10314 right now)
- Apachefriends XAMPP
- Errata Security Hamster & Ferret
- Older Fonera Fon2100 or Open-Mesh Mini-Router
- Jasager
I configured en0 (my ethernet port) for a static IP of 192.168.1.2, netmask 255.255.255.0.
My first experiment with OS X's built-in Internet sharing showed that it starts a program called natd and inserts a rule to the ipfw firewall to divert traffic through natd on port 8668. Avid BSD users are probably familiar with all of this. It's exactly how I configured my first FreeBSD home router back in the 90s. Since Internet Sharing also does a bunch of other stuff that I don't want it to do (starting a caching name server, adding a virtual IP address, and some other shenanigans) I do this stuff through the staging script instead of relying on OS X's Internet Sharing wizard. The staging script comes later on.
Also, XAMPP runs as "nobody" but a small bit of web code will need to add firewall rules, so I granted the nobody user to use ipfw without a password, via /etc/sudoers on my laptop:
nobody ALL=(ALL) NOPASSWD: /sbin/ipfwXAMPP Setup (any AMP stack will work):
Edit httpd.conf, find the line that says "Listen 80" and change it to "Listen 81" - uncomment it if needed. On OS X, this file is in /Applications/XAMPP/etc/
Create a php script that uses the $_SERVER[remote_addr] variable to modify the firewall rule set. This page will be called by a form action or link from the metasploit capture page. Mine is really simple, and I called it "control.php" in the document root. On OS X with XAMPP this is in /Applications/XAMPP/htdocs/
<?It simply redirects you to another site, and adds a rule to the firewall, telling it to skip past any rules before 2000 for your the IP address that visits this page. Since I'll be giving this demonstration at a hotel next week, the header will redirect to the hotel's web site. Since XAMPP gets finicky if it is started from the command line, you'll have to fire up the XAMPP control app and start Apache manually. MySQL and FTP need not be started for this project.
HEADER('Location: http://www.some-local-business.com/');
$cmd="sudo ipfw add 100 skipto 2000 ip from " . $_SERVER[REMOTE_ADDR] . " to any >/dev/null" ;
system($cmd);
?>

Metasploit setup:
Download and update Metasploit Framework. I prefer to get it from the subversion repository.
The HTML file that's used with the http capture module is located under the metasploit directory, then data/exploits/capture/http/index.html
The default is ugly and almost screams "you got owned!"
Staging script:
This sets up our firewall rules the way we want, prepares Hamster for use, and fires up Metasploit. Drop this script somewhere and make sure the paths are correct for Hamster and Metasploit Framework.
The default is ugly and almost screams "you got owned!"
This is what I came up with. You can view source and steal it if you want, but you can probably craft something better. Yes, it's ugly. No, I don't care. I've seen worse. Note that the "Accept" button activates the control script that I have set up on XAMPP.
Along with that is also the karma.rc - I can't remember if this one comes stock with Metasploit or not, but it's the one I use.
Staging script:
This sets up our firewall rules the way we want, prepares Hamster for use, and fires up Metasploit. Drop this script somewhere and make sure the paths are correct for Hamster and Metasploit Framework.
#!/bin/sh
sudo sysctl -w net.inet.ip.forwarding=1
sudo /usr/sbin/natd -interface en1 -use_sockets -same_ports -unregistered_only -dynamic -clamp_mss -enable_natportmap -natportmap_interface en0
sudo ipfw -f flush
sudo ipfw add 10 allow ip from 127.0.0.1 to 127.0.0.1
sudo ipfw add 1800 allow ip from 192.168.1.0/24 to 192.168.1.0/24
sudo ipfw add 1900 deny ip from 192.168.1.0/24 to any out via en1
sudo ipfw add 2000 divert 8668 ip from any to any via en1
cd ~/hamster
sudo ./hamster&
cd ~/msf
sudo ./msfconsole -r karma.rc
Fonera Setup:
This one goes together just like it did in Part 1, but a recap:
Start with a rooted and re-flashed Fon2100. I used OpenWrt 7.09 (yes, I know it's old) - Be sure to change the root password!
I then installed all of Digininja's Jasager goodies found on his site, using the tarball method. I needed a few extra packages to make everything work - I bundled them up here. Unpack them, upload them to the fon, and install them with "ipkg install *.ipk" if you need to install them.
Change the dchp server configuration to set 192.168.1.2 as the default route, and add a public DNS server, then 192.168.1.2 as the default DNS servers. I used one of Google's public DNS IP addresses for the public one. On OpenWrt 7.09, these tasks are accomplished by adding lines to /etc/dnsmasq.conf:
dhcp-option=3,192.168.1.2dhcp-option=6,8.8.8.8,192.168.1.2
If you go back to Part 1, you'll see I also did some other tweaks, like set Karma to start by default. There is a lot of information about getting Jasager up and running, but the dnsmasq configuration is the most important bit, particularly getting the public nameserver in front of the fake one we're going to fire up with Metasploit. You'll see why in just a bit.
I also changed the default SSID from "OpenWrt" to "Guest" to make it more attractive to freeloaders. You may prefer to use "linksys", "default" or any of the popular SSIDs. This is set in /etc/config/wireless.
Putting it together:
Fire up the Fonera Router
Start up XAMPP's apache server.
Run the staging script. It should come to rest at a Metasploit prompt. This is doubly fun, because it's running modules in the background to help Hamster & Ferret, but you can just as easily launch attacks from the Metasploit console if an interesting computer falls into your trap.
Browse to the Jasager interface. This should be at http://192.168.1.1:1471/ - enable KARMA mode if desired. You may wish to keep Jasager open in its own window or tab. There's usually some interesting stuff going on.
Set your browser's proxy to http://localhost:1234 to allow Hamster to inject cookies.
Browse to http://localhost:1234 and tell Ferret to watch en0 for traffic.
Here's what happens:
Victims or freeloaders connect to Jasager, and DNS resolution will hang for a few seconds because the public DNS isn't available. This DNS request will time out (usually in 5-10 seconds) and then it'll try the second DNS server in the list. That's metasploit's fake DNS server.
At this point, any service they've tried to connect to will likely get captured by Metasploit. If it's a web browser (likely) they will get roped into Metasploit's HTTP capture and they'll get our Captive portal page, complete with the iFrames that force the browser to divulge session cookies for popular websites. These iframes will also take a few seconds to resolve, but that's okay. All the while, Ferret is gathering these session ID for us.
Once the victim clicks the "Accept" button on the captive portal, the firewall rule is created that allows outbound access, including DNS. It will instantly redirect them to a website -- preferably one that's plausibly related to a nearby business. They get out, through us. Hamster catches everything. The victim is none the wiser.
Is it possible to give Evil Wifi EVEN MORE teeth?
Of course it is! You could create scripts that automatically attack new wireless clients, wrap the wireless up with SSL Strip to catch some REALLY sensitive session IDs, and any number of other malevolent things. At this point, I think I've proven how broken things are, though.
Defense?
I have plenty of thoughts on defense. There are ways to defend yourself in the wild, ways to defend your enterprise users from attacks like this, and ways that operating system vendors could prevent KARMA-style attacks from working at all. For that, you'll have to see my presentation at Security B-Sides KC. As I said at the beginning of this post, I'll have the slides uploaded and some notes posted later.




